How does a substitution cipher work
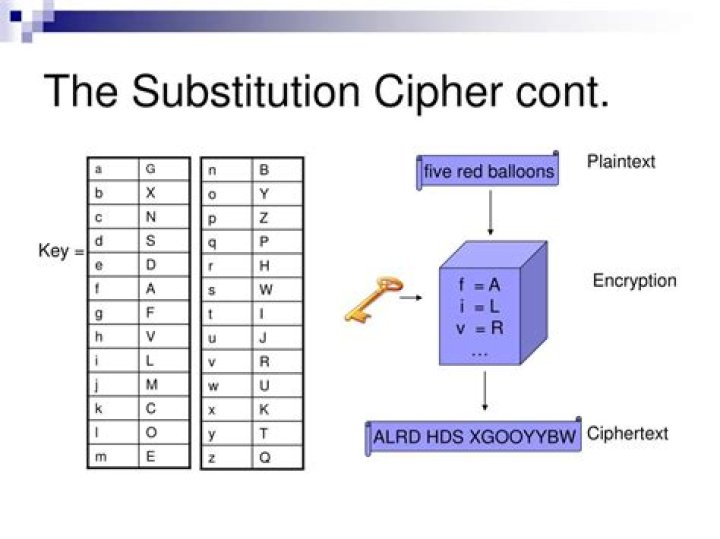
Substitution ciphers encrypt the plaintext by swapping each letter or symbol in the plaintext by a different symbol as directed by the key. … Spaces in the ciphertext are just added for readability; they would be removed in a real application of the cipher to make attacking the ciphertext more difficult.
How does a cipher work?
Ciphers, also called encryption algorithms, are systems for encrypting and decrypting data. A cipher converts the original message, called plaintext, into ciphertext using a key to determine how it is done. Asymmetric key algorithms or ciphers use a different key for encryption/decryption. …
What is substitution cipher in cryptography?
In cryptography, a substitution cipher is a method of encrypting in which units of plaintext are replaced with the ciphertext, in a defined manner, with the help of a key; the “units” may be single letters (the most common), pairs of letters, triplets of letters, mixtures of the above, and so forth.
What is the problem with a substitution cipher?
The major problem with simple substitution ciphers is that the frequencies of letters are not masked at all.What ciphers use keys?
Vigenere cipher is a poly-alphabetic substitution system that use a key and a double-entry table.
How do you crack a letter substitution cipher?
- Scan through the cipher, looking for single-letter words. …
- Count how many times each symbol appears in the puzzle. …
- Pencil in your guesses over the ciphertext. …
- Look for apostrophes. …
- Look for repeating letter patterns.
Are substitution ciphers safe?
As many a schoolboy has discovered to his embarrassment, cyclical-shift substitution ciphers are not secure, nor is any other monoalphabetic substitution cipher in which a given plaintext symbol is always encrypted into the same ciphertext symbol.
How does mixing ciphers impact the level of difficulty of decrypting the ciphertext?
How does mixing ciphers impact the level of difficulty of decrypting the ciphertext? Using a mix of ciphers makes it much harder to decrypt a ciphertext because if there is just one cipher, if you find the key to one letter, you can apply it to the entire message.Why is substitution cipher not secure?
A monoalphabetic cipher is one where each symbol in the input (called the “plaintext”) is mapped to a fixed symbol in the output (called the ciphertext). Such ciphers can easily be broken in a long list of different ways, which is why we say they are not secure.
Is substitution cipher symmetric or asymmetric?The two types of traditional symmetric ciphers are Substitution Cipher and Transposition Cipher.
Article first time published onIs Caesar Cipher a substitution cipher?
The Caesar cipher is based on transposition and involves shifting each letter of the plaintext message by a certain number of letters, historically three, as shown in Figure 5.1. … This type of encryption is known as a substitution cipher, due to the substitution of one letter for another in a consistent fashion.
Is a password a key?
A password is a user created secret phrase that is used to verify identity or generate cryptographic keys. A key is data that is used to lock and unlock cryptographic functions such as encryption, authentication and authorization.
How does a null cipher work?
In a null cipher, the plaintext is included within the ciphertext and one needs to discard certain characters in order to decrypt the message. Most characters in such a cryptogram are nulls, only some are significant, and some others can be used as pointers to the significant ones.
Who invented substitution cipher?
In about 1467 Leon Battista Alberti created the first known polyalphabetic substitution cipher. The Alberti Cipher used a mixed alphabet for encryption, which would switch to a different ciphertext alphabet at random points in the text.
Why is it easy to break Monoalphabetic ciphers?
The reason why such Ciphers can be broken is the following: Although letters are changed the underlying letter frequencies are not! If the plain letter “a” occurs 10 times its cipher letter will do so 10 times. Therefore, ANY Monoalphabetic Cipher can be broken with the aid of letter frequency analysis.
What is the primary weakness of a substitution cipher of a Caesar cipher?
The basic idea of a substitution cipher is a simple one: take one letter in your message, let’s say ‘A’, and replace it with a different letter, such as ‘E’. Sounds familiar? Both the Atbash and Caesar ciphers used this basic principle, however they both have one weakness: predictability.
What is the hardest cipher to crack?
- Australia’s Somerton Man. …
- The MIT Cryptographic ‘Time-Lock’ Puzzle – LCS35. …
- Dorabella Cipher. …
- The Voynich Manuscript. …
- The Code Book. …
- Kryptos at the CIA HQ. …
- Zodiac Killer. …
- The Beale Papers. Progress has been made solving Beale’s second cipher.
Which ciphers can be easily broken by frequency analysis?
In cryptography, frequency analysis is the study of the frequency of letters or groups of letters in a ciphertext. The method is used as an aid to breaking substitution ciphers (e.g. mono-alphabetic substitution cipher, Caesar shift cipher, Vatsyayana cipher). … This will help us decrypt some of the letters in the text.
Which cipher is hardest to break using frequency analysis?
Explanation: Out of the given options playfair cipher is the hardest cipher to break using frequency analysis. It is because it does not substitute letters of the word individually but it encrypts them in pairs of two. 7. Playfair cipher is harder to crack than keyword cipher.
How many possible keys exist for a substitution cipher?
The number of keys possible with the substitution cipher is much higher, around 2^88 possible keys.
How were the Rongorongo texts different from most other written forms of language?
This differs from almost all written forms of languages today that have characters representing only sounds or only letters. Rongorongo texts contain a mixture of symbols and a phonetic alphabet written in a unique style known as reverse boustrophedon (Ager).
What is substitution technique?
Substitution technique is a classical encryption technique where the characters present in the original message are replaced by the other characters or numbers or by symbols.
Which of the following is substitution cipher?
Which of the following is a type of substitution cipher? Explanation: In substitution cipher the plain text is replaced by cipher text according to a fixed rule. There are two types of substitution cipher – Mono alphabetic and Poly alphabetic cipher.
What is the difference between substitution cipher and transposition cipher?
Substitution ciphers differ from transposition ciphers. In a transposition cipher, the plaintext is repositioned, but the letters are left unchanged. In contrast, a substitution cipher maintains the same sequence of the plaintext and modifies the letters themselves.
Why is Stream cipher not secure?
Another problem with stream ciphers is that they provide no authentication and thus are vulnerable to “bit-flipping” attacks. … Stream ciphers are dangerous to use with stored data, or if the key is used more than once. Stream ciphers are vulnerable to “key re-use” attacks, also called “two-time pad” attacks.
Can a block cipher act as a stream cipher?
In some cases, block ciphers can operate as stream ciphers based on their modes of operation.
What do you understand by transposition and substitution?
The substitution and transposition techniques are used for converting a plaintext into ciphertext, where substitution technique replaces the characters whereas transposition technique rearranges the characters to form a ciphertext. However, a substitution cipher is simpler and easy to break.
Are all block ciphers Polyalphabetic explain?
Block ciphers work in a way similar to polyalphabetic ciphers, with the exception that a block cipher pairs together two algorithms for the creation of ciphertext and its decryption. … Each algorithm uses two inputs: a key and a “block” of bits, each of a set size.
Is shift cipher a substitution cipher?
Just as Caesar ciphers are a subset of shift ciphers, shift ciphers are a subset of substitution ciphers. In a substitution cipher, each letter of the alphabet is mapped to another letter of the alphabet for encryption. For example, the encrypted value of A might be M, while B might be Q.
What cipher did the Romans use?
The Caesar Cipher is a basic technique for encryption. It substitutes certain letters of the alphabet for others so that words aren’t immediately recognizable. Named for Julius Caesar, a Roman emperor who used it, the Caesar Cipher is also called the Caesar Shift or Shift Cipher.
Why is it called Caesar cipher?
The Caesar cipher is named after Julius Caesar, who, according to Suetonius, used it with a shift of three to protect messages of military significance: … While Caesar’s was the first recorded use of this scheme, other substitution ciphers are known to have been used earlier.